Documentation Index
Fetch the complete documentation index at: https://docs.envzero.com/llms.txt
Use this file to discover all available pages before exploring further.
Using OpenID Connect Tokens
OpenID Connect (OIDC) allows your deployments to exchange short-lived tokens directly from your cloud provider. env zero provides an OIDC token (JWT) as an environment variable. A deployment can use this to access compatible cloud services without a long-lived credential stored in env zero.Enabling OIDC Token Availability
A JWT token could be available during deployment as an environment variable calledENV0_OIDC_TOKEN.
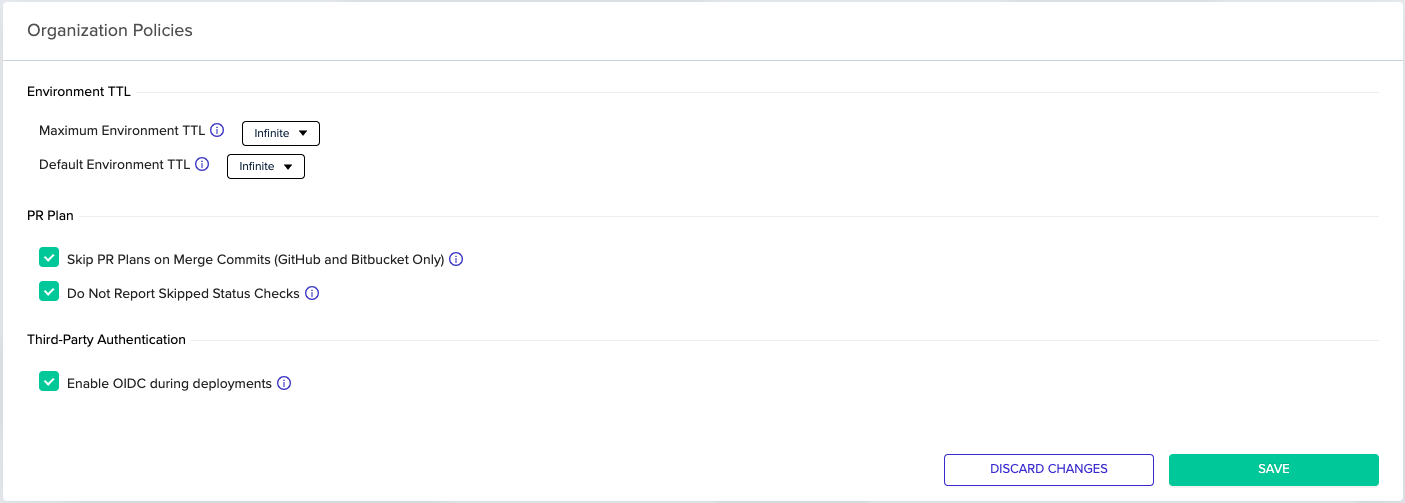
This feature can be enabled by selecting an OIDC credential when creating a credential in the organization’s credentials page.In addition, organization admins can enable this feature by toggling the related checkbox in the organization’s policies tab.
Setting Up Your 3rd Party Service Integration
Consult your 3rd party service’s documentation for how to add an identity provider.For example, Vault’s JWT Authentication, or AWS’s Creating OpenID Connect (OIDC) identity providers. The OIDC token is unique to your organization. The custom claims attached to the token contain your organization ID. You can find your env zero organization ID by navigating to the Organization Settings page in our web app and copying the UUID from the URL. In addition, the OpenID Connect ID tokens issued by env zero have a fixed audience (see
aud in the table below).
Format of the OpenID Connect ID token
The OpenID Connect ID token contains the following standard claims.| Claims | Description |
|---|---|
iss | The issuer. The issuer is specific to env zero and the value is: https://login.app.env0.com/ |
sub | The subject. It contains the user ID that represents your organization’s OIDC user. If you like to get this ID please contact us |
aud | The audience. This is a fixed string value: https://prod.env0.com |
iat | The time of issuance. This is when the token was created, which is shortly before the deployment starts. |
exp | The expiration time. Its value is 24 hours after the time of issuance. |
| Additional Claims | Description |
|---|---|
apiKeyType | The value should be oidc. Claim that the provided JWT should be from type oidc only |
organizationId | Unique organization ID |
projectId | Unique project ID |
projectName | Project name |
templateId | Unique template ID |
templateName | Template name |
environmentId | Unique environment ID |
environmentName | Environment name |
workspaceName | Workspace name |
deploymentLogId | Unique deployment ID |
deploymentType | Deployment type such as deploy, destroy, prPlan, or task. See the full list. |
deployerEmail | Email of the person that triggered the deployment |
env0Tag | User-controlled free-form string (when ENV0_OIDC_TAG environment variable is set). Informational context only, not an identity claim. See Using claims in IAM trust policies. |
Specific AWS Session Tags:
In addition to the claims mentioned above, there is also a specific section for AWS tags inside ahttps://aws.amazon.com/tags and inside principal_tags:
| Additional Claims | Description |
|---|---|
https://aws.amazon.com/tags[principal_tags][organizationId] | Unique organization ID |
https://aws.amazon.com/tags[principal_tags][projectId] | Unique project ID |
https://aws.amazon.com/tags[principal_tags][templateId] | Unique template ID |
https://aws.amazon.com/tags[principal_tags][environmentId] | Unique environment ID |
https://aws.amazon.com/tags[principal_tags][deployerEmail] | Email of the person that triggered the deployment |
https://aws.amazon.com/tags[principal_tags][deploymentType] | Deployment Type |
https://aws.amazon.com/tags[principal_tags][env0Tag] | User-controlled free-form string. Informational context only, not safe as an IAM trust condition. See Using claims in IAM trust policies. |
Custom Claims
You can add a custom claim to the OIDC token by setting theENV0_OIDC_TAG environment variable in env zero.
Usage:
- Set
ENV0_OIDC_TAGas an environment variable in env zero. - The value is included in the token as both
env0Tagandhttps://env0.com/env0Tagclaims. - For AWS integrations, it is also included in the
https://aws.amazon.com/tagsprincipal_tags.
ENV0_OIDC_TAG=production-workload, the token includes:
Using claims in IAM trust policies
Becauseenv0Tag is user-controlled, it is not safe as an authorization gate. Use system-issued claims (organizationId, projectId, environmentId, templateId) for IAM trust conditions instead, and keep env0Tag for informational use only.
The examples below use aws:PrincipalTag/<claim>. aws:RequestTag/<claim> is also valid in AWS trust policies and can be used interchangeably for these conditions.
Unsafe vs. safe examples
Unsafe,env0Tag is user-controlled:
ENV0_OIDC_TAG=my-secret-string can assume this role.
Safe, bind to immutable org identity:
Which claims are safe for trust conditions?
| Claim | Source | Safe as IAM trust condition? |
|---|---|---|
organizationId | env zero | Yes. Immutable, unique per tenant. |
projectId | env zero | Yes. Immutable, scopes to a single project. |
environmentId | env zero | Yes. Immutable. |
templateId | env zero | Yes. Immutable. |
deployerEmail | env zero | Use with care. Immutable per deploy but the org can change who deploys. Combine with organizationId. |
env0Tag | End user | No. Never as a sole condition. Informational context only. |
JWT Verification
JWT signatures will be verified against public keys from the issuer.A JSON Web Key Set (JWKS) URL should be configured on your 3rd party service side.
Keys will be fetched from this endpoint during authentication.
Our JWKS URL is:
https://login.app.env0.com/.well-known/jwks.json
Next steps
- OIDC for AWS - Configure OIDC authentication for AWS environments.
- OIDC for Azure - Configure OIDC authentication for Azure environments.
- OIDC for GCP - Configure OIDC authentication for GCP environments.
- OIDC for Vault - Use OIDC tokens to authenticate with HashiCorp Vault.