Documentation Index
Fetch the complete documentation index at: https://docs.envzero.com/llms.txt
Use this file to discover all available pages before exploring further.
Introduction
This guide will detail the various steps required to integrate OneLogin as a SAML provider for your env zero organization. The current implementation supports SAML 2.0 and is used for authentication only, where you define your users in your OneLogin account to enable them access to your env zero organization. You can also add env zero as an application in your user application dashboard.Self-Service Configuration Available: You can configure SAML SSO directly from your organization settings. See Self-Service SSO Integration for an overview, or Self-Service SAML Setup for step-by-step instructions.
Steps
- Login to your OneLogin Administrator account.
- Under the Application tab go to the Application.
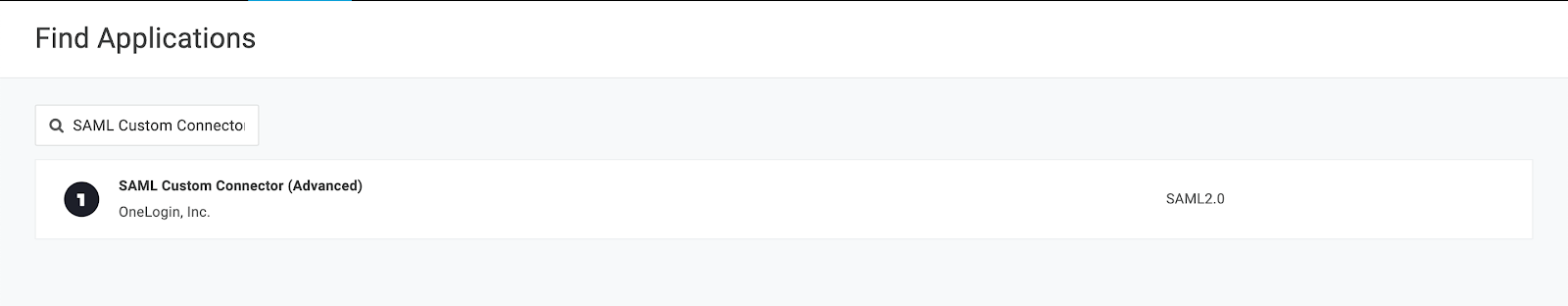
- Click on the
Add Appbutton. - In the search box enter
SAML Custom Connectorand selectSAML Custom Connector (Advanced)
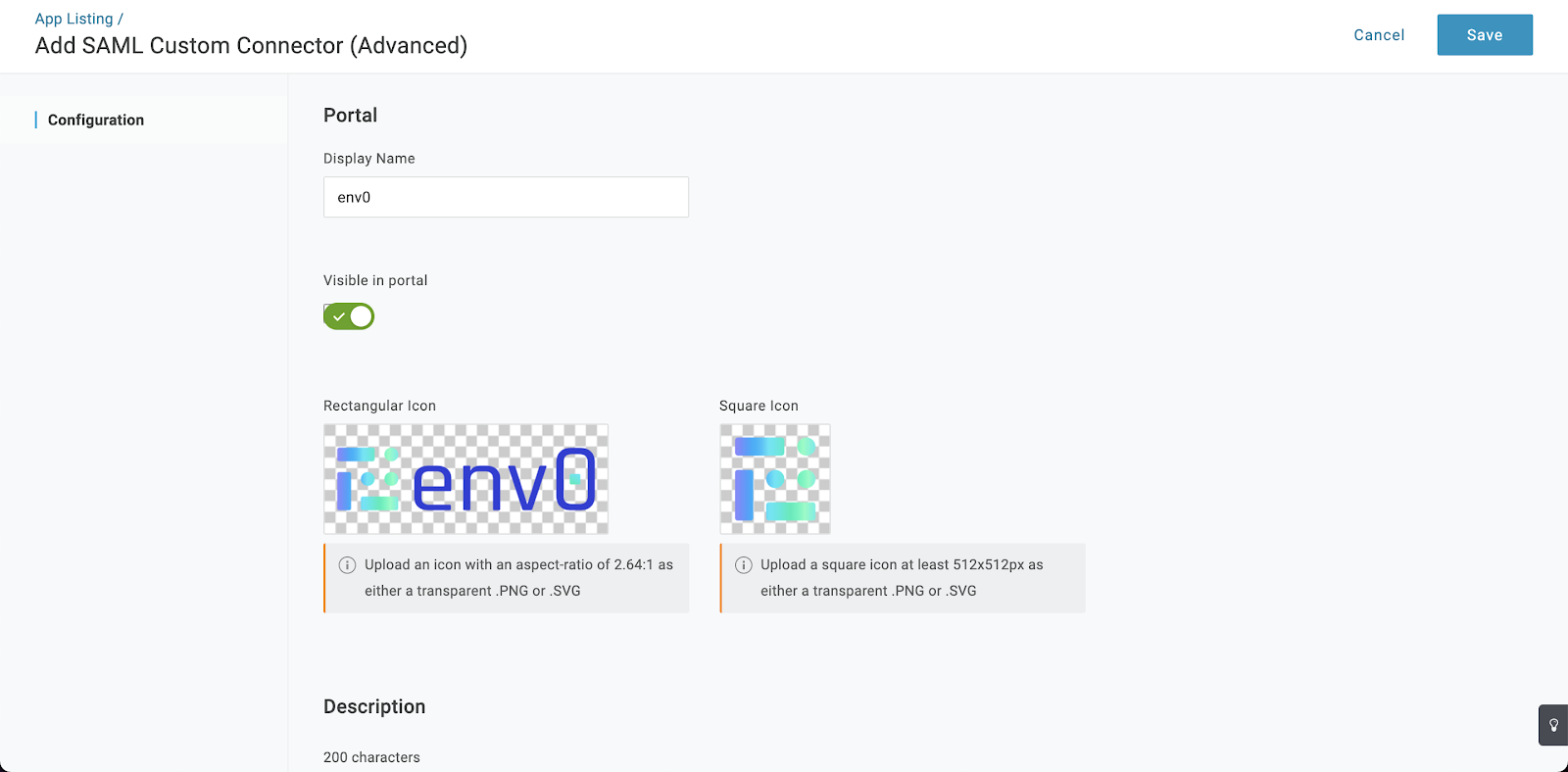
- Change the display name to be
env zeroand upload an icon. - Enter a relevant description and click on the save button.
- Go to the configuration tab.
- Under Audience (EntityID) enter
urn:auth0:env0:{YOUR_ENV0_ORG_ID} - Under ACS (Consumer) URL Validator enter:
[-a-zA-Z0-9@:%._\+~#=]{2,256}\.[a-z]{2,6}\b([-a-zA-Z0-9@:%_\+.~#?&//=]*) - Under ACS (Consumer) URL enter
https://login.app.env0.com/login/callback?connection={YOUR_ENV0_ORG_ID} - Under the Login URL enter
https://app.env0.com/login/sso - In the
SAML initiatordropdown selectService Provider - In the
SAML nameID formatdropdown selectUnspecified - In the
SAML signature elementdropdown selectBoth - Click on the save button.
- Go to the “Parameters” tab
- Add the following Parameters:
| Name | Marco | Value | Include in SAML assertion |
|---|---|---|---|
| NameID value | false | N/A | |
| false | true | ||
| firstName | false | First Name | true |
| lastName | false | Last Name | true |
| name | true | true |
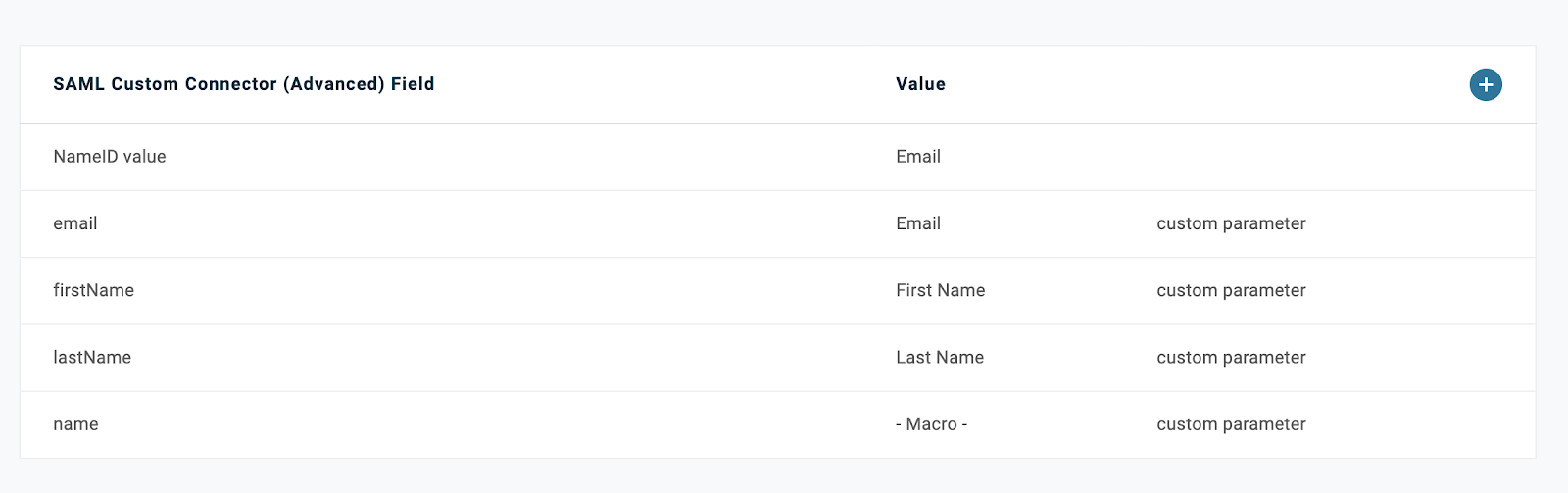
- Click on the
Savebutton. - Go to the
SSOtab. - Copy the
SAML 2.0 Endpoint (HTTP)URL. - Copy the
SLO Endpoint (HTTP)URL. - In the
X.509 Certificateclick on theView Detailslink. - Under the
X.509 CertificatechooseX.509 PEMand download it. - Assign the relevant users to this application.
- Navigate to your env zero organization settings and go to the SSO tab.
- Click on SAML and complete the self-service form with:
- Identity Provider Single Sign-on URL (SAML 2.0 Endpoint (HTTP) URL)
- X.509 Certificate
Next steps
- Self-Service SAML Setup - Review the general SAML configuration process.
- Sync Roles & Groups From Your IdP - Import OneLogin groups into env zero.
- Azure Active Directory Integration - Compare with another supported identity provider.